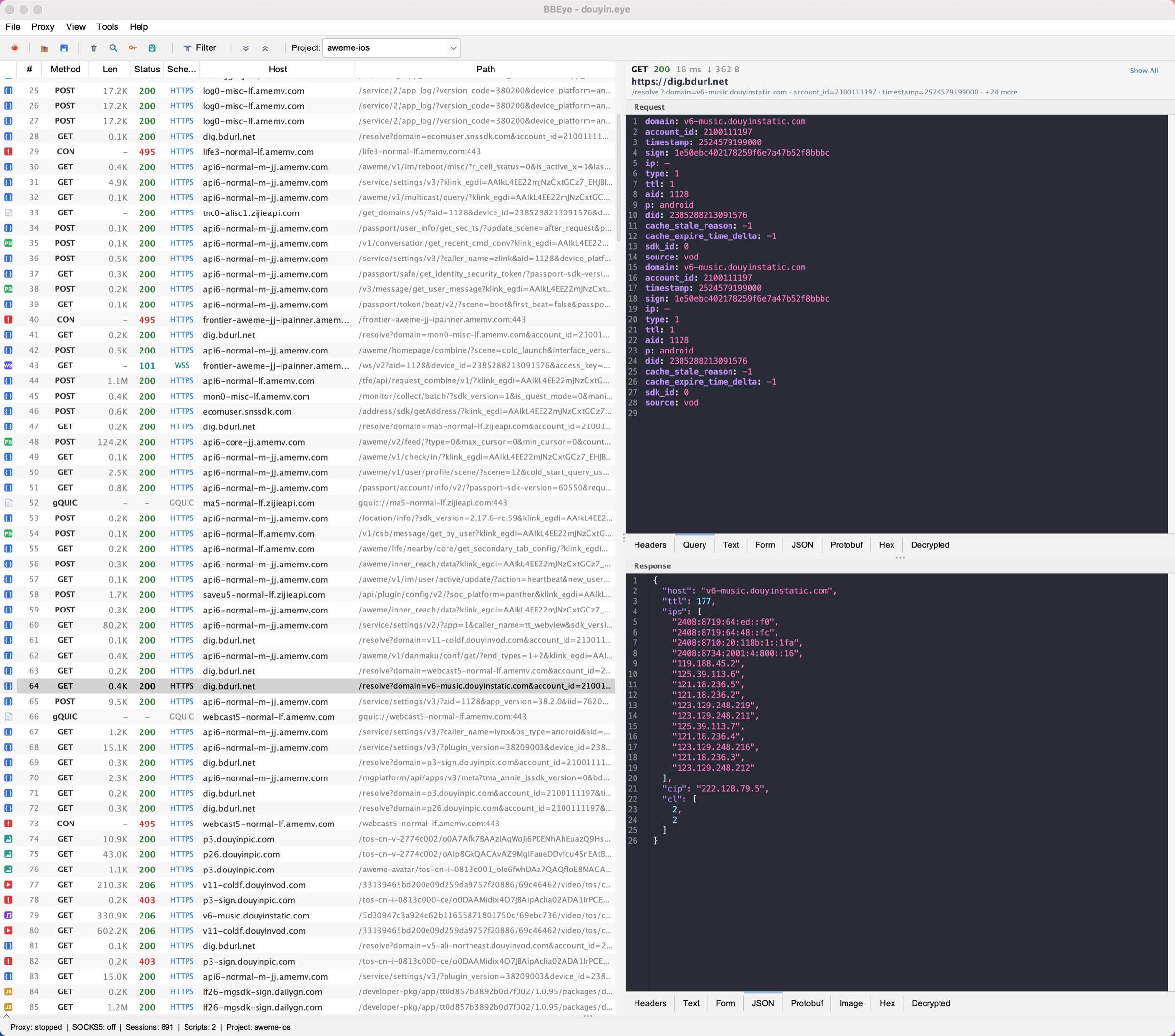
Full Protocol Capture
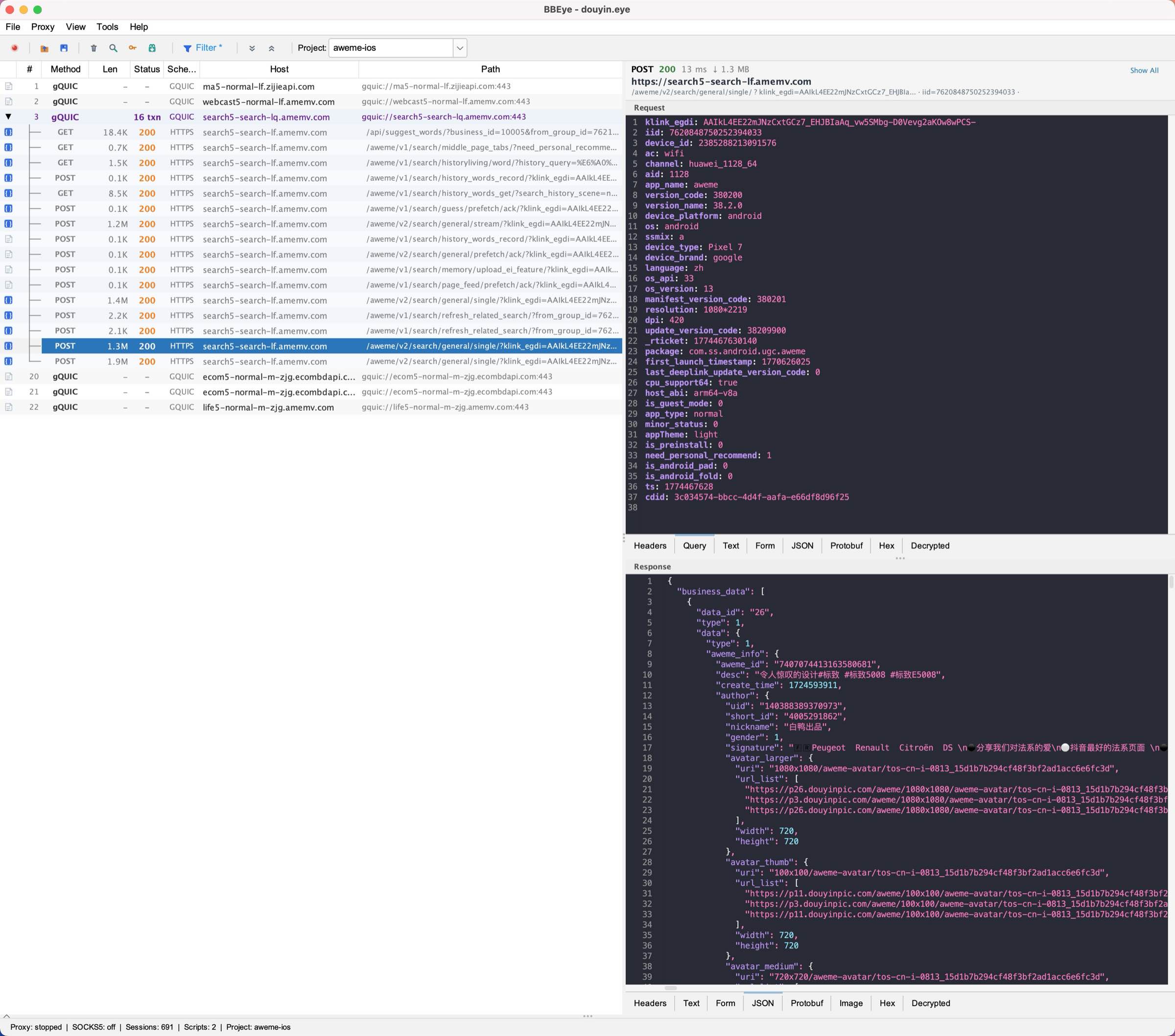
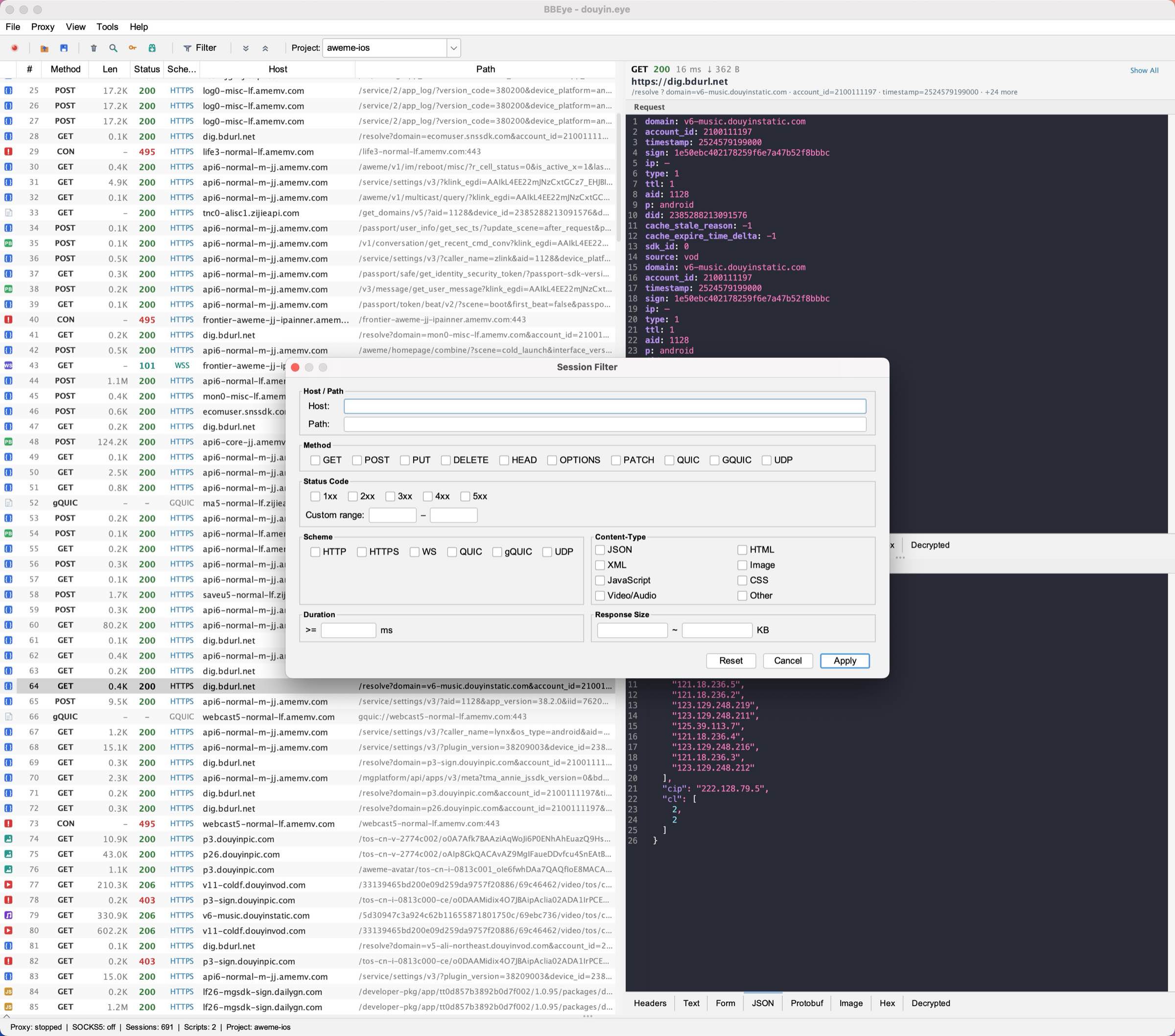
Capture and inspect all traffic in real-time. Tree-structured session list, JSON syntax highlighting with 20+ color themes, and intelligent content rendering for headers, forms, protobuf, and hex.
Intercept, decrypt, and analyze network traffic across every protocol. Built for reverse engineers and security researchers.
Capture and inspect all traffic in real-time. Tree-structured session list, JSON syntax highlighting with 20+ color themes, and intelligent content rendering for headers, forms, protobuf, and hex.
SOCKS5 and HTTP proxy in one. The mixed port mode routes both TCP and UDP connections through BBEye, enabling QUIC and UDP traffic interception that traditional HTTP proxies miss entirely.
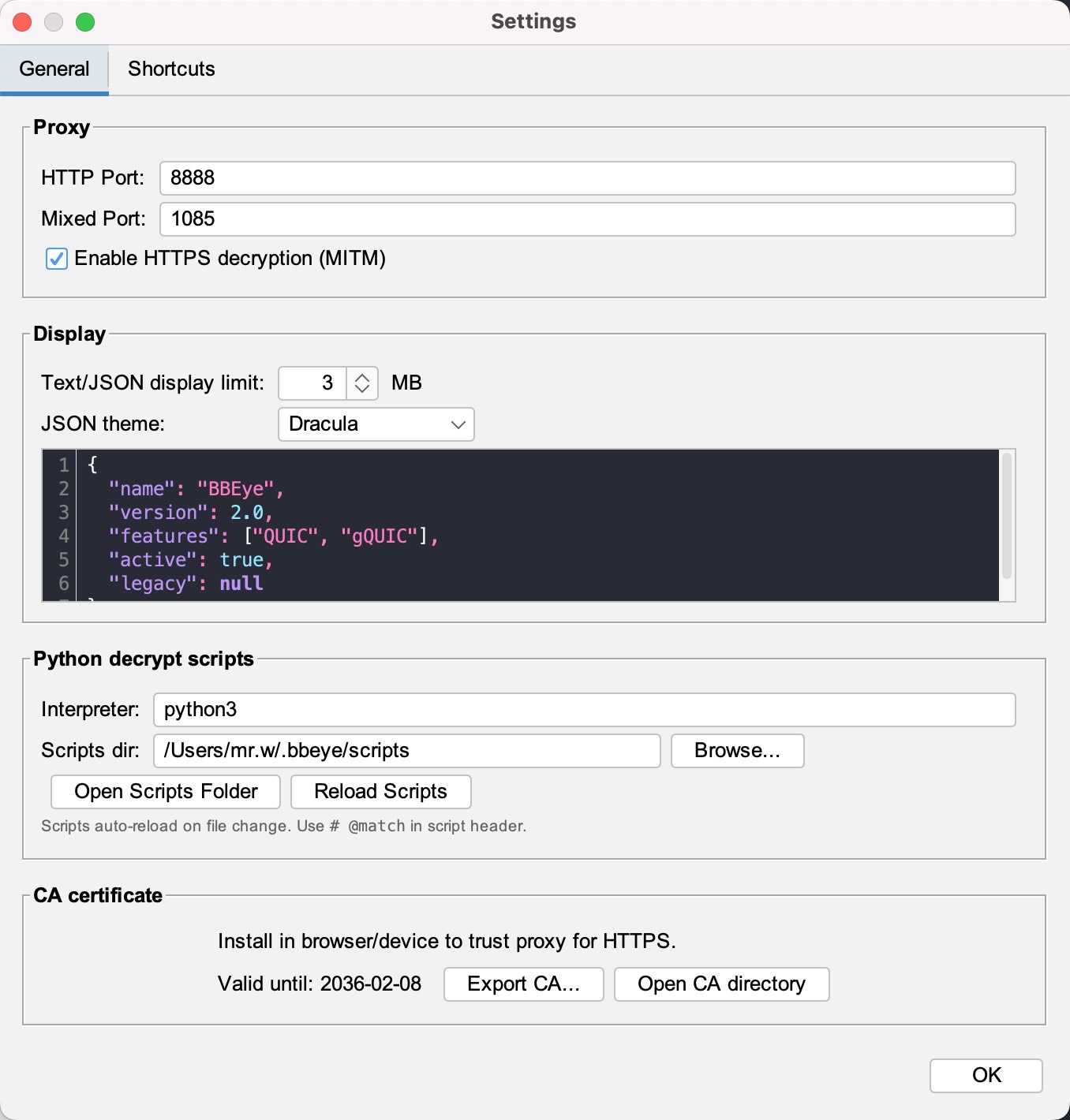
Full decryption of gQUIC (Q043/Q046/Q050) and IETF QUIC. Three-phase key derivation: initial, diversified, and forward-secure. HTTP/2 stream reassembly with HPACK header decompression.
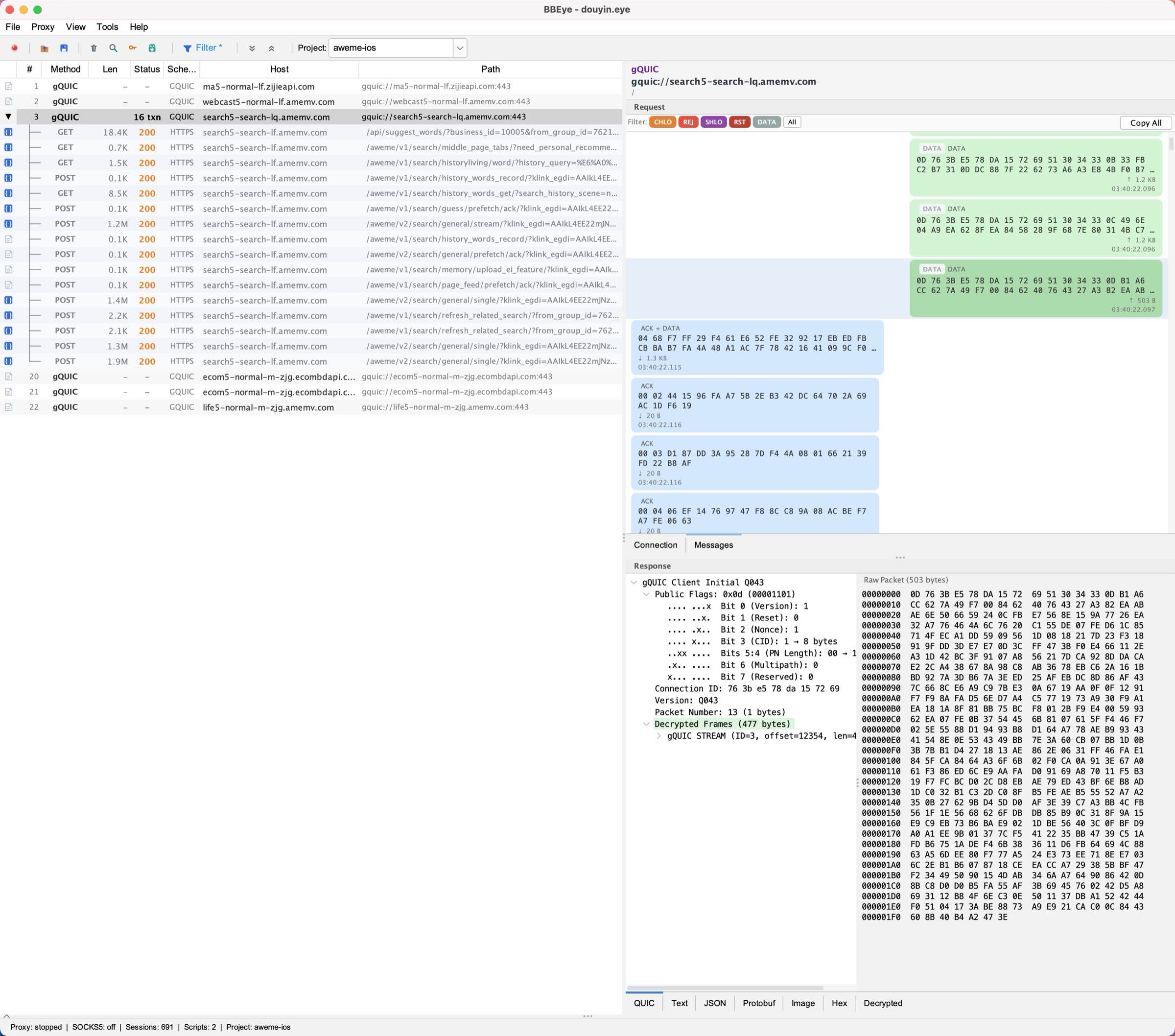
After key import and stream reassembly, gQUIC traffic is fully decoded into standard HTTPS sessions. JSON responses are pretty-printed with syntax highlighting and searchable in the viewer.
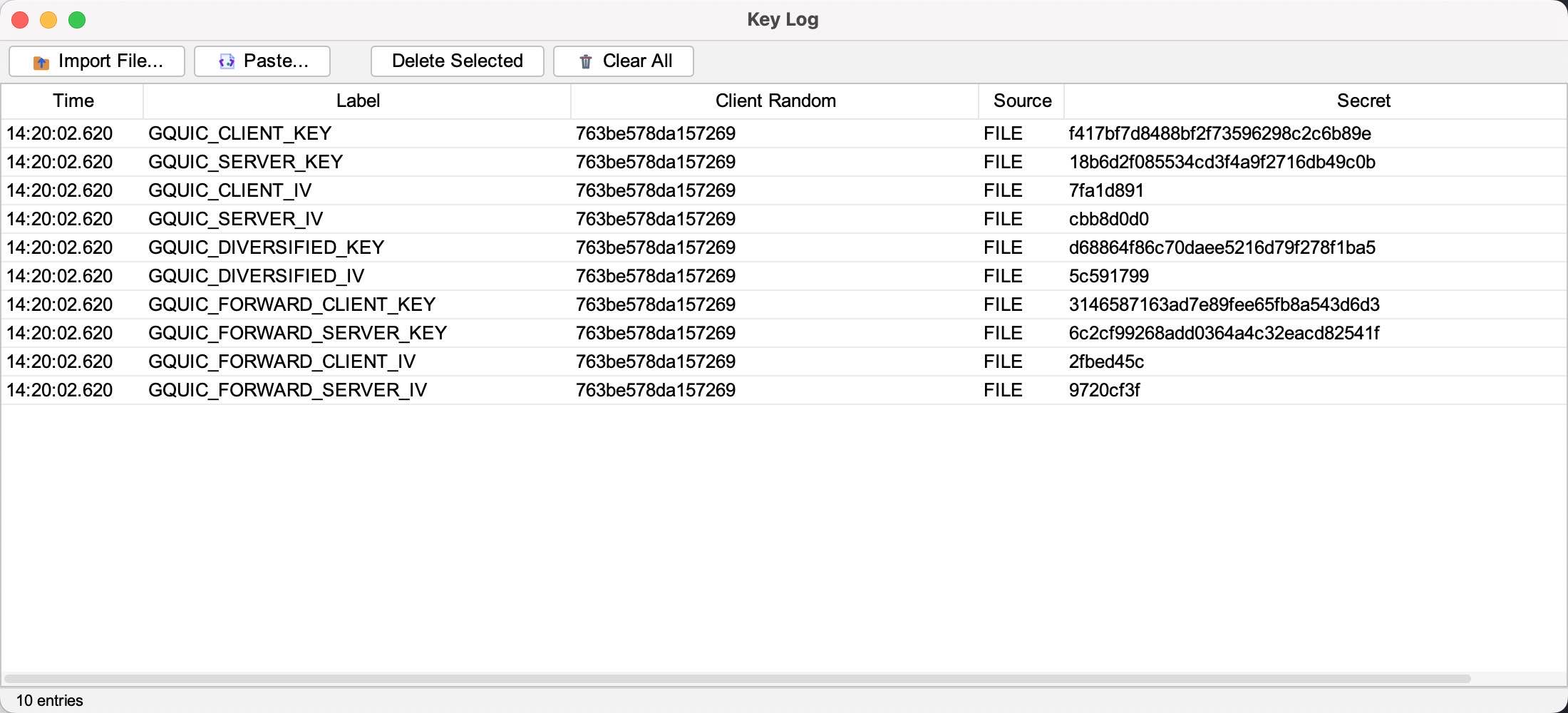
Import NSS Key Log files or receive keys in real-time via Frida hooks. Supports TLS 1.2 CLIENT_RANDOM, TLS 1.3 traffic secrets, and all gQUIC key phases including diversified and forward-secure keys.
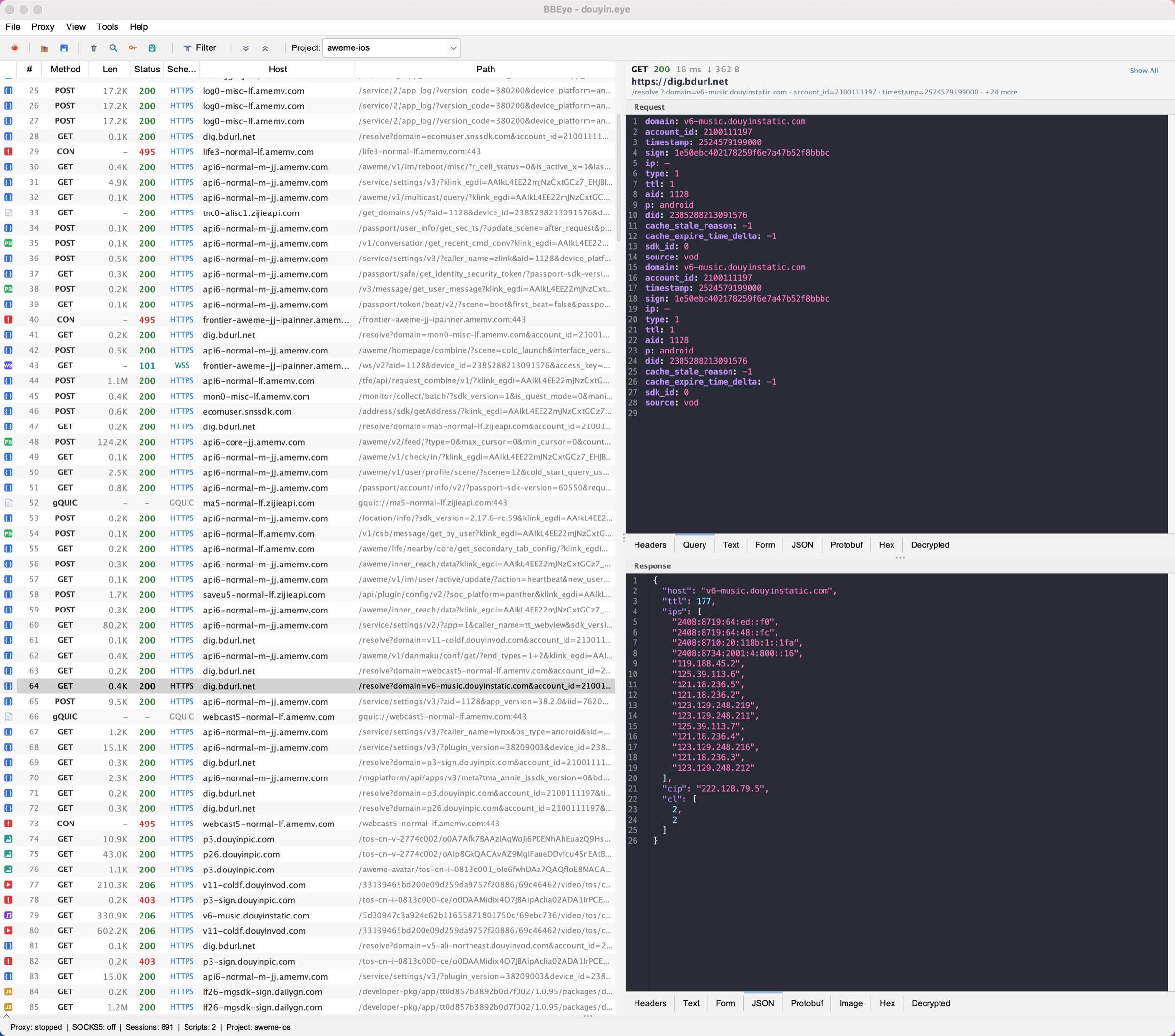
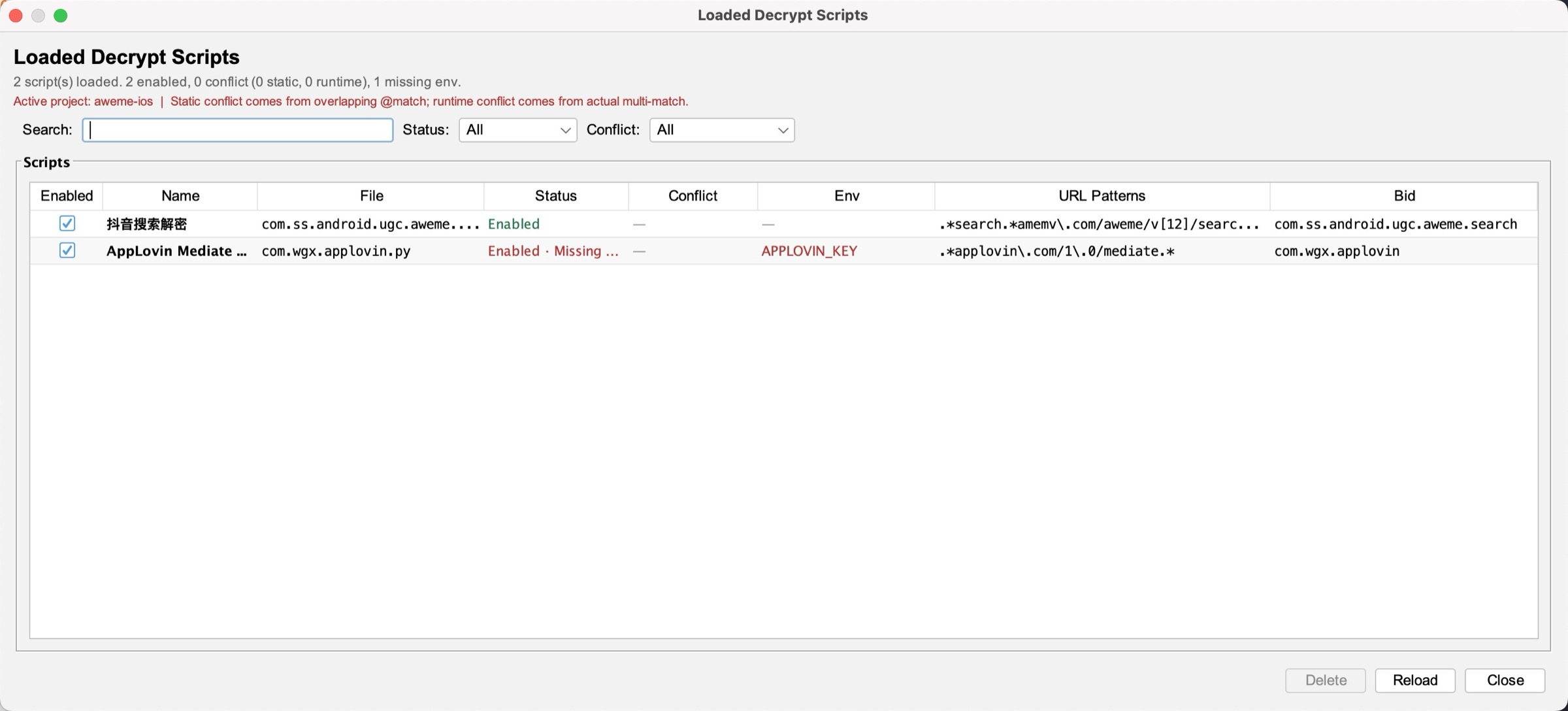
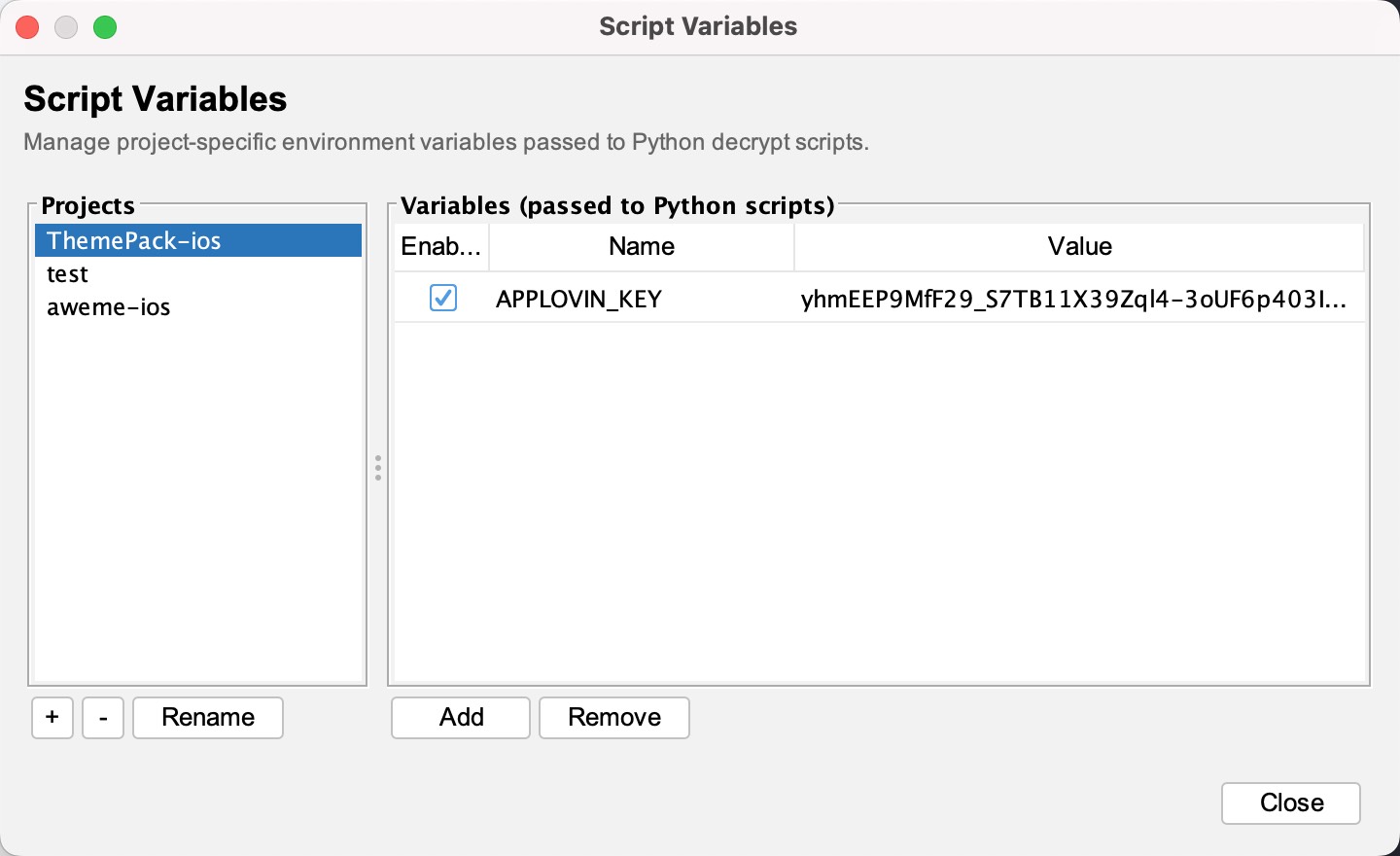
Write custom Python scripts to decrypt encrypted API responses. URL pattern matching, environment variable injection, and real-time reload on file change.
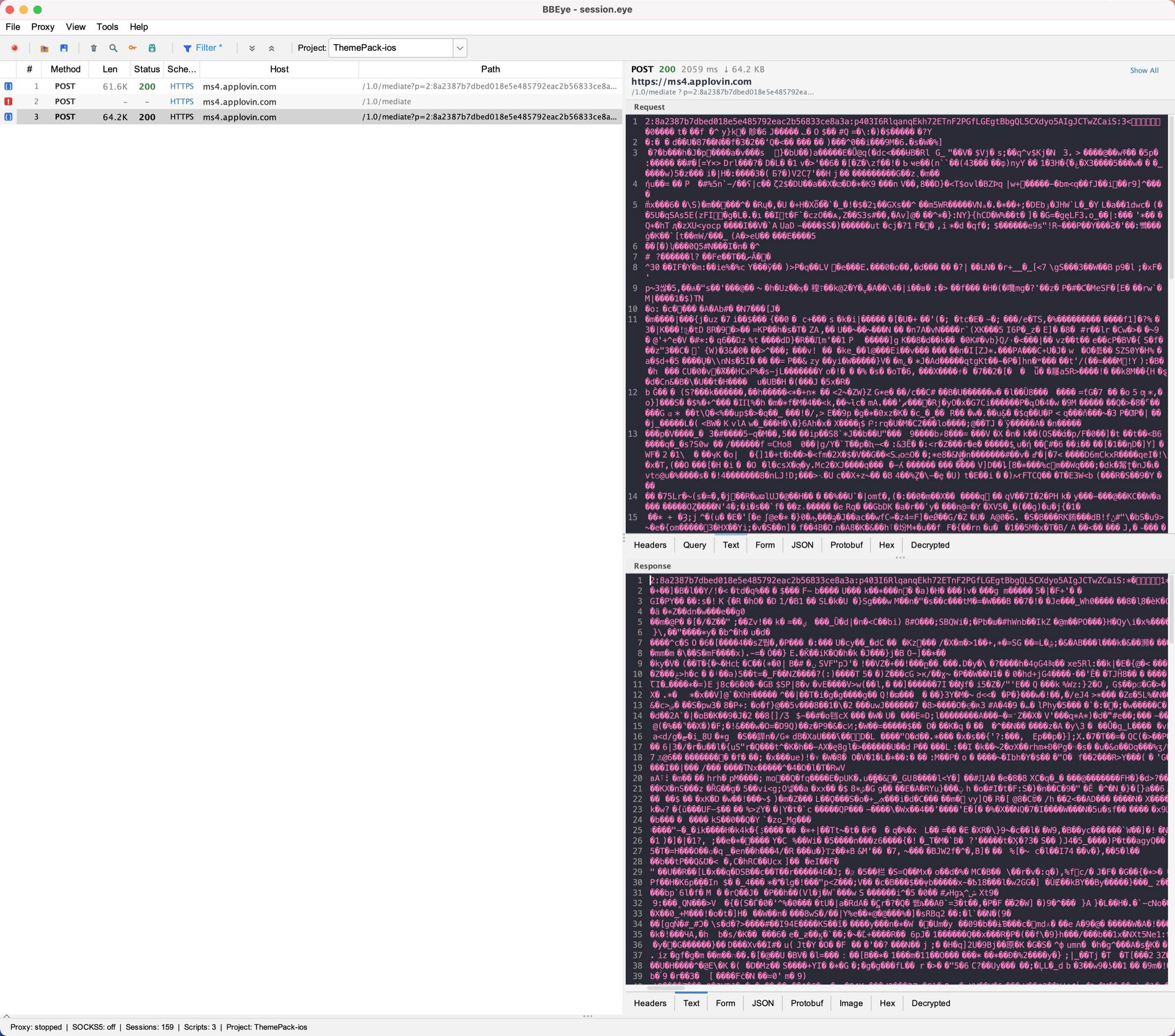
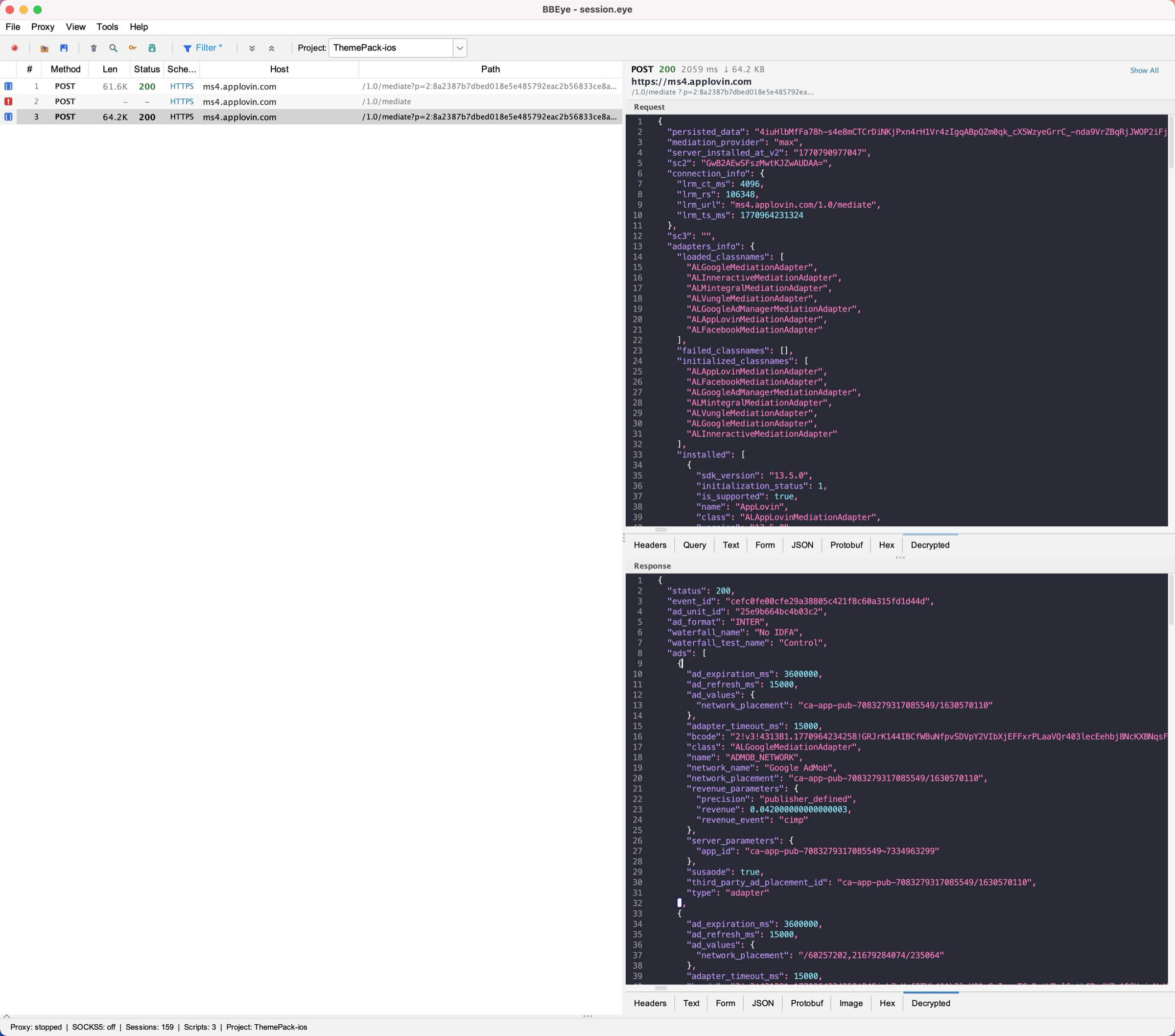
Manage decrypt scripts with @match URL patterns, conflict detection, and environment variable dependencies. Scripts auto-reload on file change — no restart required.
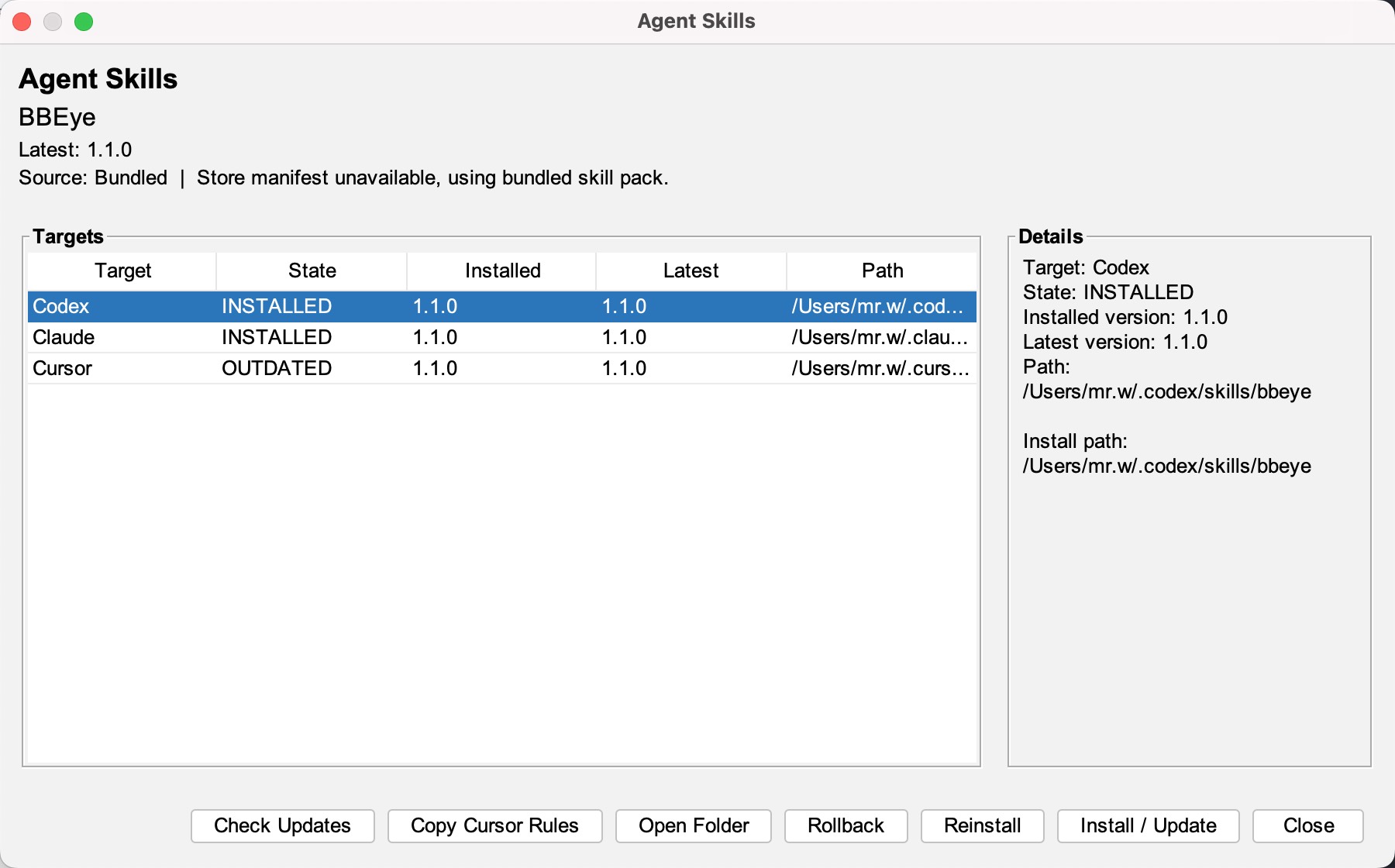
Built-in skill packs for Claude Code, Cursor, and Codex. One-click install lets AI agents consume captured traffic in real-time via the live directory API at ~/.bbeye/live/.
Isolate work by project. Each project has its own set of environment variables passed to decrypt scripts. Switch between projects instantly.
Filter sessions by host, path, method, status code, content type, duration, and response size. Supports HTTP, HTTPS, WebSocket, QUIC, gQUIC, and UDP protocol filtering.
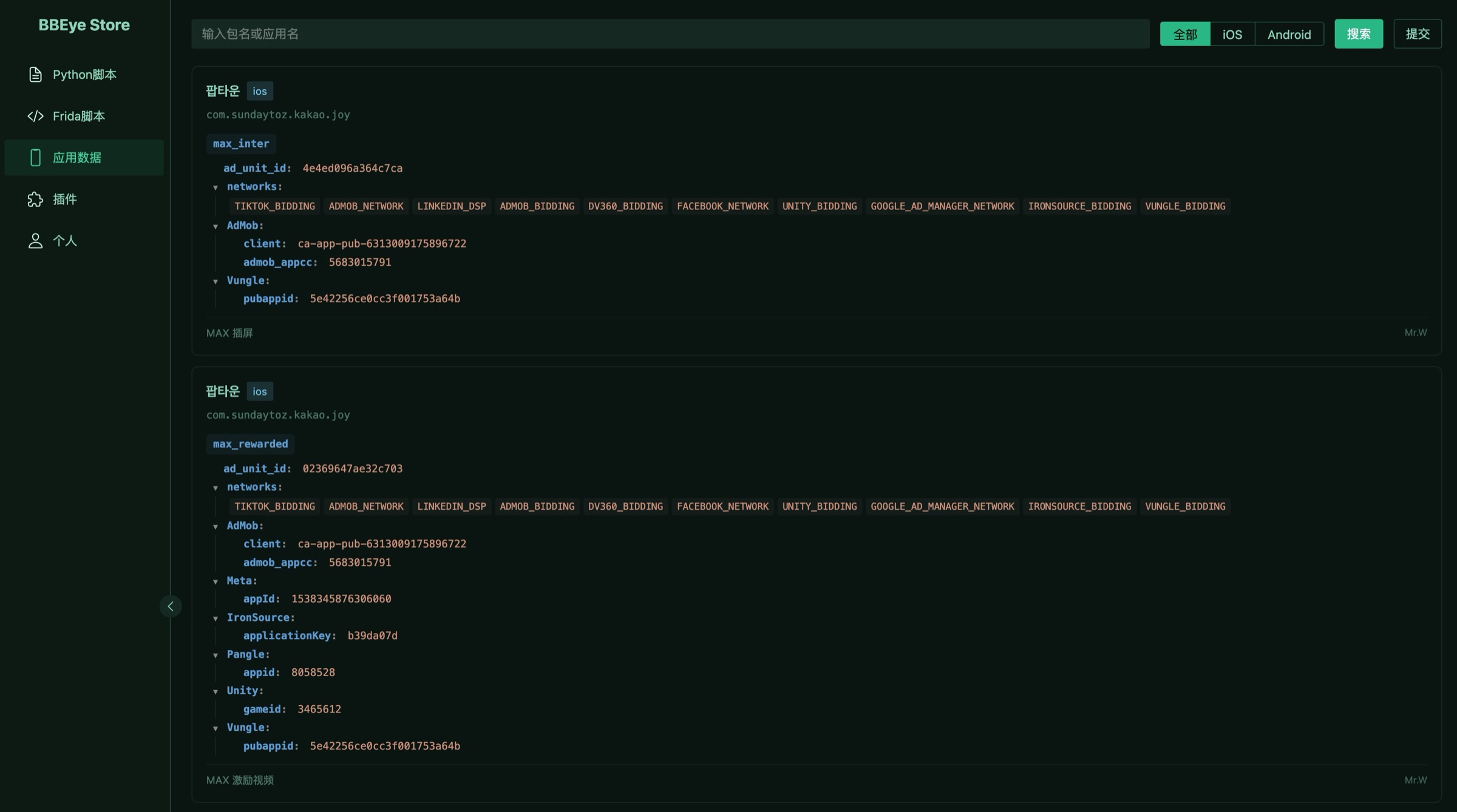
Community-driven script marketplace. Share and discover decrypt scripts, Frida hooks, plugins, and AppData configurations. Search by app name, package, or platform.
Initial, diversified (HKDF + nonce), and forward-secure key derivation. Full AES-128-GCM decryption pipeline.
HPACK header decompression, stream offset tracking, and multi-frame DATA reassembly for complete request/response reconstruction.
Automatic Brotli, gzip, and deflate decompression based on Content-Encoding headers. Transparent to scripts and viewers.
Xcode Dark, Monokai, Dracula, Nord, Cyberpunk, and more. RSyntaxTextArea-powered rendering with sub-300ms load for 2MB+ JSON.
Real-time session export to ~/.bbeye/live/ with atomic index.json writes. Designed for AI agent consumption and external tool integration.
ZIP-based session archive preserving all metadata, request/response bodies, QUIC packets, WebSocket frames, and key log entries.
支持。BBEye 是少数能完整抓包和解密 gQUIC(Q043/Q046/Q050)及 IETF QUIC 协议的工具。通过 Frida hook 导出 Key Log,配合三阶段密钥解密(Initial → Diversified → Forward-Secure),实现 QUIC 流量的完整解密和 HTTP/3 重组。
Yes. BBEye supports everything Charles does (HTTP/HTTPS MITM, SSL proxying, request editing) plus QUIC/UDP capture, Python script decryption, 20+ JSON themes, and AI Agent integration — features Charles doesn't offer.
BBEye 提供 HTTP 代理(端口 8888)和 SOCKS5 代理(Mixed Port 1085)。手机设置代理后即可捕获 HTTP/HTTPS 流量。对于 QUIC/UDP,通过 SOCKS5 的 UDP ASSOCIATE 功能配合 mihomo 等客户端实现。支持 Frida hook 绕过证书固定(SSL Pinning)。
HTTP, HTTPS, WebSocket, gQUIC (Q043/Q046/Q050), IETF QUIC v1/v2, HTTP/3, UDP, SOCKS5. BBEye captures and decrypts traffic across all major protocols used by modern apps including TikTok, Instagram, and other apps using QUIC.
Wireshark 是被动抓包工具,无法解密 HTTPS。mitmproxy 是命令行 MITM 代理,不支持 QUIC。BBEye 结合了两者优势:图形界面 + MITM 解密 + QUIC/UDP 捕获 + Python 脚本扩展 + AI Agent 集成,是专为逆向工程和安全研究设计的一体化工具。
BBEye uses NSS Key Log format with custom gQUIC extensions. Keys are exported via Frida hooks on BoringSSL (GQUIC_CLIENT_KEY, GQUIC_FORWARD_SERVER_KEY, etc.). The tool performs HKDF key derivation, AES-128-GCM decryption, HTTP/2 HPACK header decompression, and Brotli/gzip body decompression automatically.